Level-Up your MFA: Why SMS Codes Are No Longer Enough

For years, enabling Multi-Factor Authentication (MFA) has been a cornerstone of account and device security. While MFA remains essential, the threat landscape has evolved, making some older methods less effective. The most common form of MFA, four- or six-digit codes sent via SMS, is convenient and familiar, and it’s certainly better than relying on passwords […]
How to Spot Hidden Malware on Your Devices

Malware is a harmful software that can damage devices, steal data, and slow performance. It spreads through unsafe downloads, phishing emails, and malicious websites. Signs include sluggish performance, pop-ups, and high data usage. Protect yourself by using antivirus software, updating software, avoiding suspicious links, and practicing good cybersecurity habits.
Navigating CAN/CIOSC Security Compliance

CAN/CIOSC 104:2021 is a Canadian national standard outlining baseline cybersecurity controls for small and medium-sized organizations. It provides a tiered approach (Levels 1 and 2) to implementing these controls, progressing from basic security practices to more advanced measures.
Embracing AI: How Businesses Can Thrive with Ethical Adoption

The 2024 Work Trend Index reveals AI’s growing role in workplaces, emphasizing ethical use, employee collaboration, and upskilling. Businesses adopting AI effectively can enhance productivity, attract talent, and navigate transformation successfully.
Navigating the Challenges of Data Lifecycle Management

Data is one of the most valuable assets a business can have. Managing this data throughout its lifecycle can be challenging. Data lifecycle management (DLM) refers to several processes and policies. They govern the handling, storage, and eventual disposal of data. Businesses generate and store vast amounts of data. As this happens, the importance of […]
The Technologies Shaping the Future of Customer Experience

Discover how cutting-edge technologies like AI, omnichannel support, and self-service platforms are reshaping customer service, boosting efficiency, personalization, and satisfaction to meet evolving customer expectations and stay competitive.
6 Simple Steps to Enhance Your Email Security

Email is a fundamental communication tool for businesses and individuals alike. But it’s also a prime target for cybercriminals. Cyberattacks are increasing in sophistication. This means enhancing your email security has never been more critical. Ninety-five percent of IT leaders say cyberattacks have become most sophisticated. Over half (51%) have already seen AI-powered attacks in […]
Remote Work, Real Risks: A Guide to Keeping Your Team Secure

Learn practical cybersecurity strategies to keep your remote team secure, including network protection, safe browsing habits, and training. Overcome the increased risks remote work presents and safeguard your business.
Phishing 2.0: How AI is Amplifying the Danger and What You Can Do

AI-driven phishing, or “Phishing 2.0,” uses realistic, personalized messages and automation to increase success rates. Traditional detection methods struggle, making it harder to protect against these sophisticated and dangerous attacks.
The Essential Role of Continuous Monitoring in Cybersecurity | Advanced Threat Defense & Proactive Security
Don’t skimp on continuous cybersecurity monitoring—think of it as your digital watchdog. It catches vulnerabilities and alerts you before hackers can exploit them. It’s essential for real-time threat response, regulatory compliance, and overall peace of mind.
Enhance Cybersecurity Posture with NIST CSF 2.0 Framework

Staying ahead of threats is a challenge for organizations of all sizes. Reported global security incidents grew between February and March of 2024. They increased by 69.8%. It’s important to use a structured approach to cybersecurity. This helps to protect your organization. The National Institute of Standards and Technology (NIST) created a Cybersecurity Framework (CSF). […]
Unlocking the True Value of New Technology: Comprehensive Training and Change Management

New tech is exciting but can be a financial nightmare if you skip employee training and change management. Without these, productivity drops, errors increase, and morale plummets. Invest in training and clear communication for smooth transitions.
10 Tips for Building a Cyber-Aware Culture in Your Organization

Cyberattacks are a constant threat, often due to employee error. Building a strong culture of cyber awareness can significantly reduce risks. Leadership buy-in, engaging training, and fostering security champions are key steps.
The Rise of Email Authentication: Why DMARC Matters for Your Business

Email authentication is crucial in combating phishing scams, which are a major security threat. Learn about DMARC, Google and Yahoo’s new policies, and how to protect your business from email spoofing.
The Dangers of Using an Administrator Account as Your Normal User Account

Using an admin account for everyday tasks is a risky move. It makes your system more vulnerable to malware and accidental changes. Stick to a standard user account for better security.
Transform Your Business with Effective Data Management

Data is the lifeblood of modern businesses, driving insights and decision-making. However, poor data management can lead to inefficiency, compliance issues, and poor customer satisfaction. This guide outlines best practices and strategies to transform your data management, enhancing operational efficiency, decision-making, and customer experience.
2024 Data Security Trends: AI, Ransomware, and Zero Trust

Cyber threats are evolving fast, so staying ahead is crucial. AI and machine learning are making waves, ransomware is getting more targeted, and early data governance is key. Zero Trust and biometrics are also hot topics. Get a security assessment to stay protected!
Beware of Deepfakes! Learn How to Spot the Different Types
Deepfakes, using AI to create fake media, can mislead and deceive, with potential for serious abuse. Spot them by checking inconsistencies, sources, and seek verification. Stay informed and critical.
Introducing the New Microsoft Planner (Everything You Need to Know)

Microsoft’s new Planner is revolutionizing task management by combining collaboration features and simplicity with AI-powered insights, offering a one-stop solution for anything from everyday tasks to enterprise projects, all accessible via Teams or a web browser.
Tactics to Reduce Cloud Waste at Your Business

Cloud computing’s perks – scalability, flexibility, cost-efficiency – are dampened by 32% of spend wasted on unused services. Tackling this through audits, right-sizing, reserved instances, and automation can slash costs, boost efficiency, and curtail unnecessary spend. Contact us for expert help in optimizing your cloud usage.
2023 Annual Cybersecurity Attitudes and Behaviors Report

In an online-centric world, almost 90% of data breaches stem from human error. The latest report underlines the widespread digital presence and security challenges, noting that while most find cybersecurity crucial, many feel overwhelmed. Training and best practices, like using unique passwords and multi-factor authentication, are urged to combat cybercrimes, which have affected over a quarter of respondents.
Be Careful When Scanning QR Codes

QR codes, handy for quick access to content, have a dark side with scammers using them for phishing. Fake codes may steal data, install malware, or trick you into payments. Stay vigilant: verify sources, inspect URLs before clicking, and keep devices updated. Contact us for anti-phishing solutions.
Cybersecurity Predictions for 2024

As 2024 unfolds, staying ahead in cybersecurity means prepping for AI’s dual role, looming quantum threats, rising hacktivism, persistent ransomware, and influential cyber insurance. It’s crucial to adopt a proactive, comprehensive cybersecurity strategy with regular assessments to navigate these challenges.
Workspaces, a VPN & More – Learn the Newest Microsoft Edge Features

Microsoft Edge introduces Workspaces for customized, persistent browsing environments, aiding task management and productivity. New features include form autofill, Web Capture, AI tools via Copilot, and Read Aloud for multitasking. Microsoft ensures continuous browser updates to enhance user experience.
How to set Automatic Replies in Outlook (Desktop)
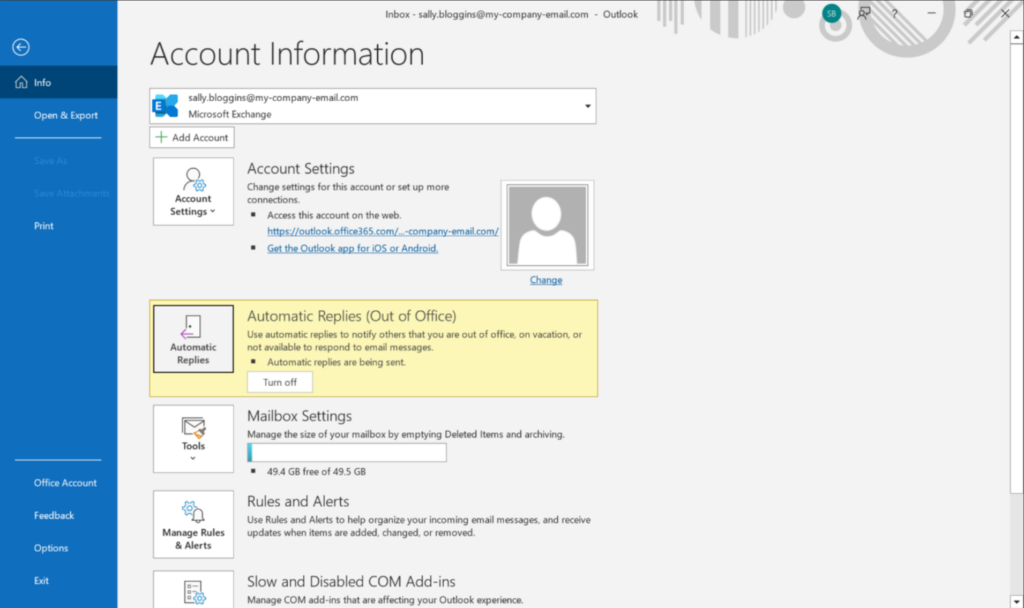
This article explains how to set your Out of Office reply in the desktop version of Microsoft Outlook.
These 7 AI Trends Are Sweeping the Cybersecurity Realm
Relentless digital innovation has defined the last few years. The symbiotic relationship between AI and cybersecurity has become pivotal especially when it comes to safeguarding sensitive information and digital assets. As cyber threats evolve in complexity, AI has emerged as a formidable ally. It empowers organizations with advanced tools and techniques. Helping them to stay […]
How to set Automatic Replies on a Shared Mailbox
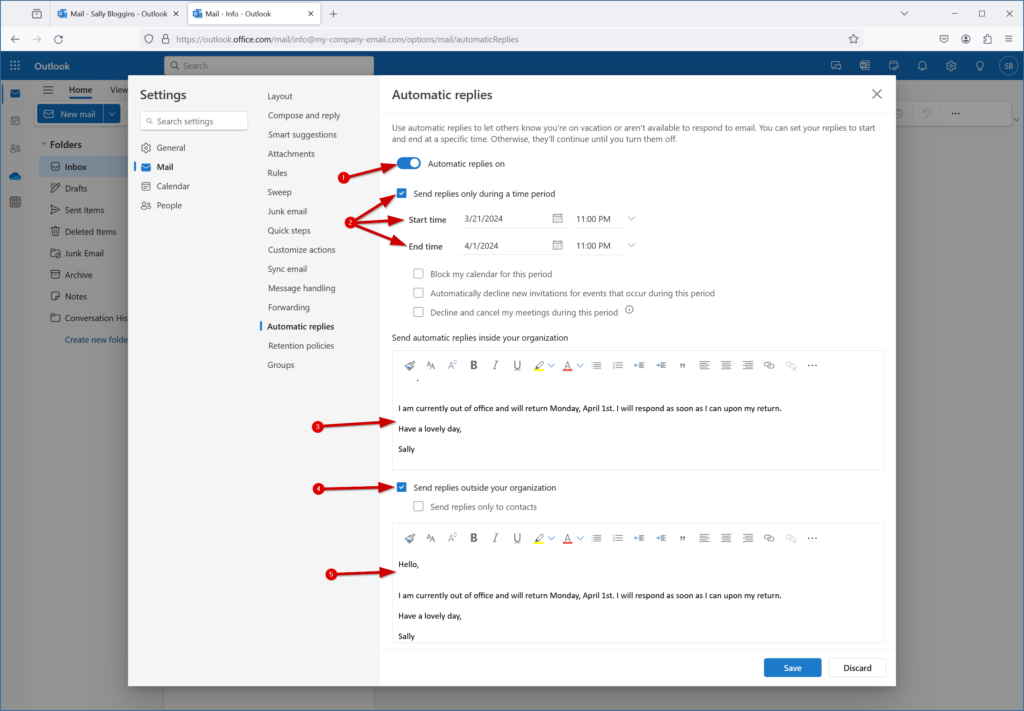
This article explains how to set an automatic reply for a Shared Mailbox.
Online Security: The Dangers of Browser Extensions

Browser extensions have become as common as mobile apps. People tend to download many and use few. There are over 176,000 browser extensions available on Google Chrome alone. These extensions offer users extra functionalities and customization options. While browser extensions enhance the browsing experience, they also pose a danger which can mean significant risks to […]
How Small Businesses Are Unlocking Growth With Generative AI

Staying ahead in business often means embracing cutting-edge technologies. New tools can unlock new avenues for growth especially for small businesses. SMBs are often looking for affordable ways to gain a competitive advantage. One such transformative force is Generative Artificial Intelligence (GenAI). This is a technology that goes beyond automation and the AI we used […]
Examples of How a Data Breach Can Cost Your Business for Years

In the digital age, data is the lifeblood of businesses. It fuels operations, decision-making, and customer interactions. But there is a dark underbelly of this data-centric landscape. It’s the persistent threat of data breaches. The repercussions of a data breach extend far beyond the immediate aftermath. They often haunt businesses for years. Only 51% of […]
Demystifying web accessibility: insights and best practices for your website

Over two thirds of adults with disabilities use computers and smartphones, making web accessibility crucial. Organizations must create inclusive websites, starting with understanding impairments ranging from cognitive to motoric. Adopt principles like perceivable content, operable navigation, assistive technology integration, and regular accessibility audits to ensure a frictionless experience for all, enhancing legal compliance, reach, and sales.
Are Your Smart Home Devices Spying On You?

The integration of smart home devices has become synonymous with modern living. They offer convenience, efficiency, and connectivity at our fingertips. But a recent study has raised concerns about the darker side of these smart gadgets. It suggests that our beloved smart home devices may be spying on us. It’s natural these days to invite […]
5 Ways to Leverage Microsoft 365’s New AI Innovations
Microsoft 365 has a powerful suite of cloud-based productivity tools. They can help you work smarter and faster. Microsoft has consistently been at the forefront of innovation. M365 was one of the very first all-in-one cloud tools, introduced as Office 365 in 2013. Now, Microsoft and its business tools are at the leading edge of […]
